Azure Defender provides security alerts and advanced threat protection for all kinds of workloads, like virtual machines, SQL databases, containers and web applications. New plans within Azure Defender are regularly introduced, recently for Key Vault and now also for DNS (and Resource Manager, see link).
Azure Defender for DNS provides an additional layer of protection for your cloud resources by continuously monitoring all DNS queries from your Azure resources and runs advanced security analytics to alert you when suspicious activity is detected.
Azure Defender for DNS protects against issues including:
- Data exfiltration from your Azure resources using DNS tunneling.
- Malware communicating with command and control server.
- Communication with malicious domains as phishing and crypto mining.
- DNS attacks—communication with malicious DNS resolvers.
And all of that without using any agents. All you have to do is use the DNS that Azure offers and to enable the Azure Defender plan for DNS.
Alerts
A full list of the alerts provided by Azure Defender for DNS:
| Alert | Description | Intent |
| Anomalous network protocol usage (AzureDNS_ProtocolAnomaly) |
Analysis of DNS transactions from %{CompromisedEntity} detected anomalous protocol usage. Such traffic, while possibly benign, may indicate abuse of this common protocol to bypass network traffic filtering. Typical related attacker activity includes copying remote administration tools to a compromised host and exfiltrating user data from it. | Exfiltration |
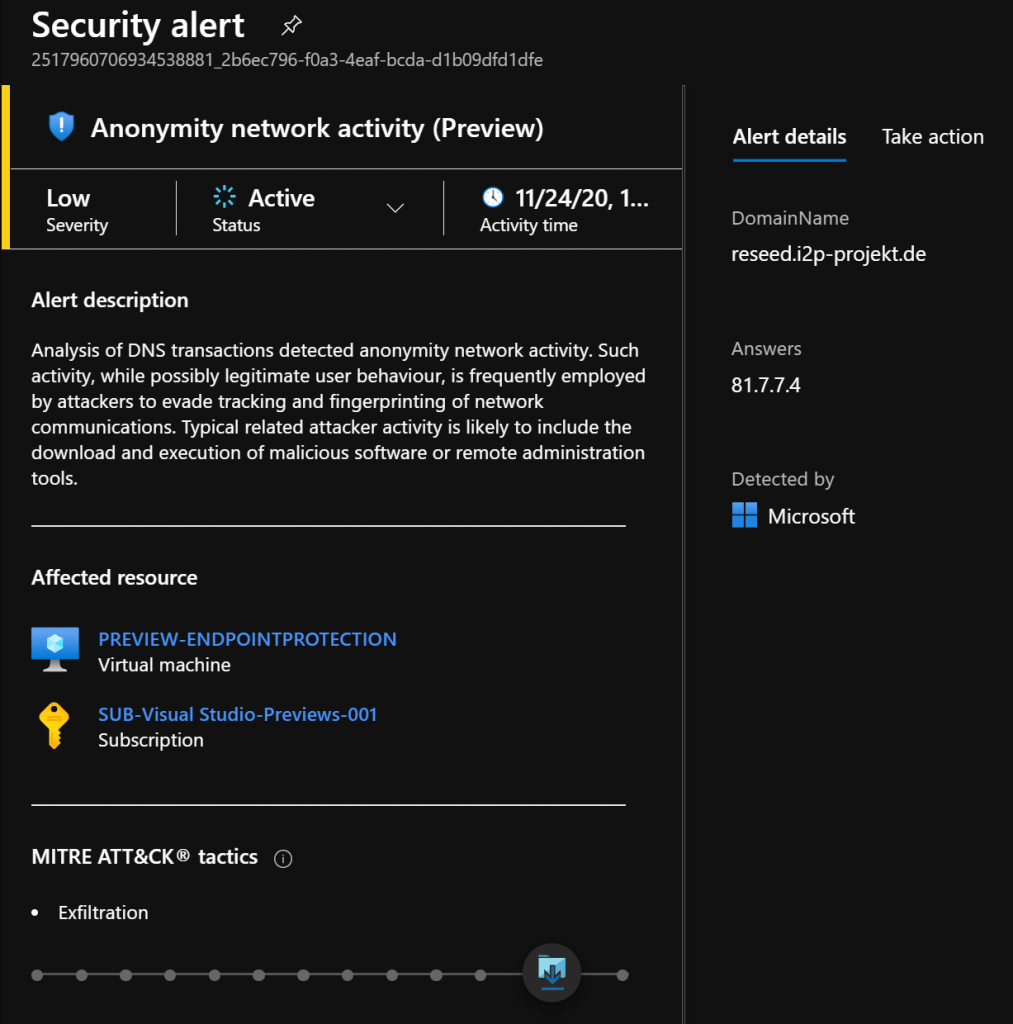
| Anonymity network activity (AzureDNS_DarkWeb) |
Analysis of DNS transactions from %{CompromisedEntity} detected anonymity network activity. Such activity, while possibly legitimate user behaviour, is frequently employed by attackers to evade tracking and fingerprinting of network communications. Typical related attacker activity is likely to include the download and execution of malicious software or remote administration tools. | Exfiltration |
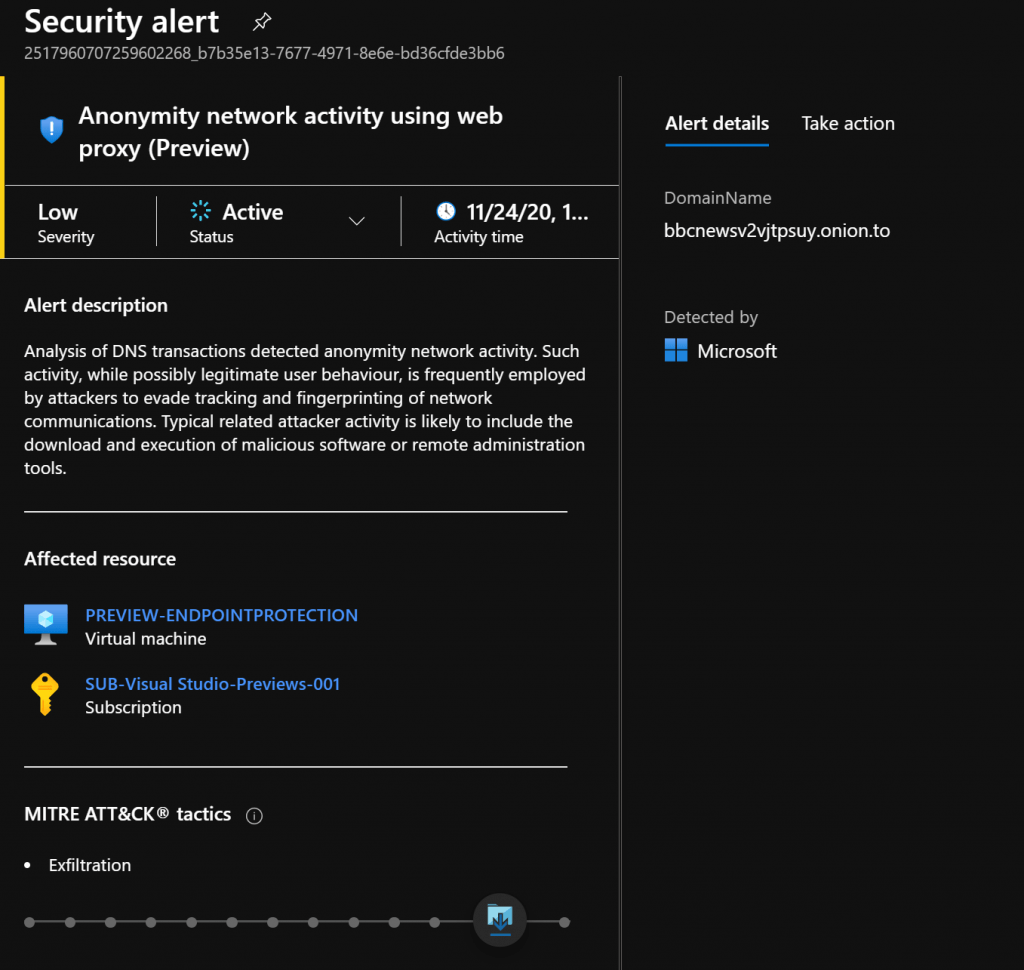
| Anonymity network activity using web proxy (AzureDNS_DarkWebProxy) |
Analysis of DNS transactions from %{CompromisedEntity} detected anonymity network activity. Such activity, while possibly legitimate user behaviour, is frequently employed by attackers to evade tracking and fingerprinting of network communications. Typical related attacker activity is likely to include the download and execution of malicious software or remote administration tools. | Exfiltration |
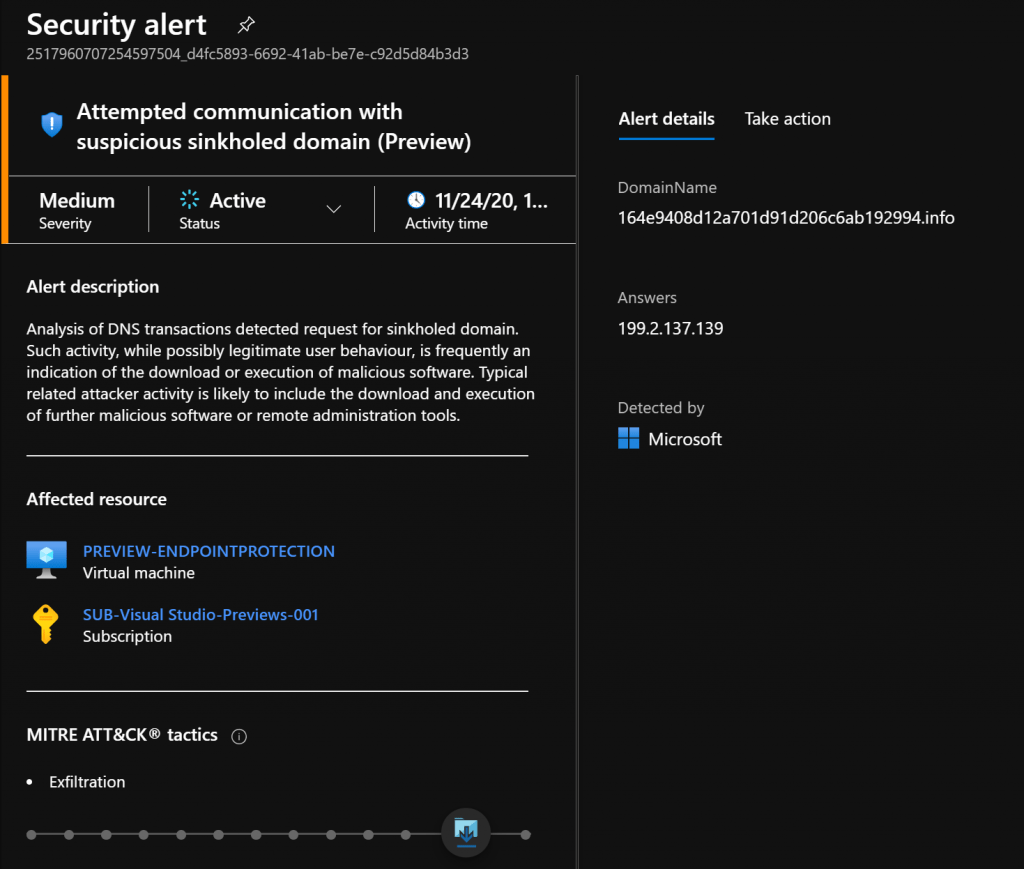
| Attempted communication with suspicious sinkholed domain (AzureDNS_SinkholedDomain) |
Analysis of DNS transactions from %{CompromisedEntity} detected request for sinkholed domain. Such activity, while possibly legitimate user behaviour, is frequently an indication of the download or execution of malicious software. Typical related attacker activity is likely to include the download and execution of further malicious software or remote administration tools. | Exfiltration |
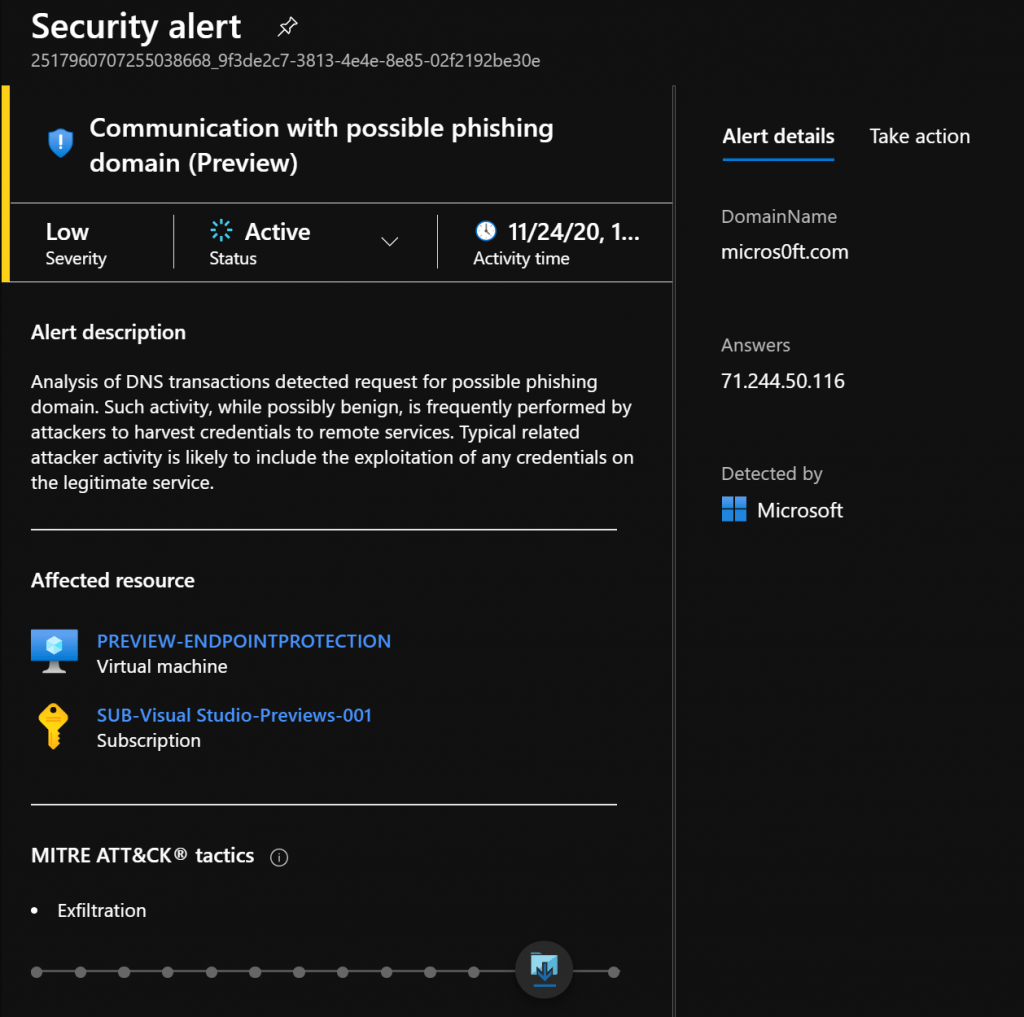
| Communication with possible phishing domain (AzureDNS_PhishingDomain) |
Analysis of DNS transactions from %{CompromisedEntity} detected a request for a possible phishing domain. Such activity, while possibly benign, is frequently performed by attackers to harvest credentials to remote services. Typical related attacker activity is likely to include the exploitation of any credentials on the legitimate service. | Exfiltration |
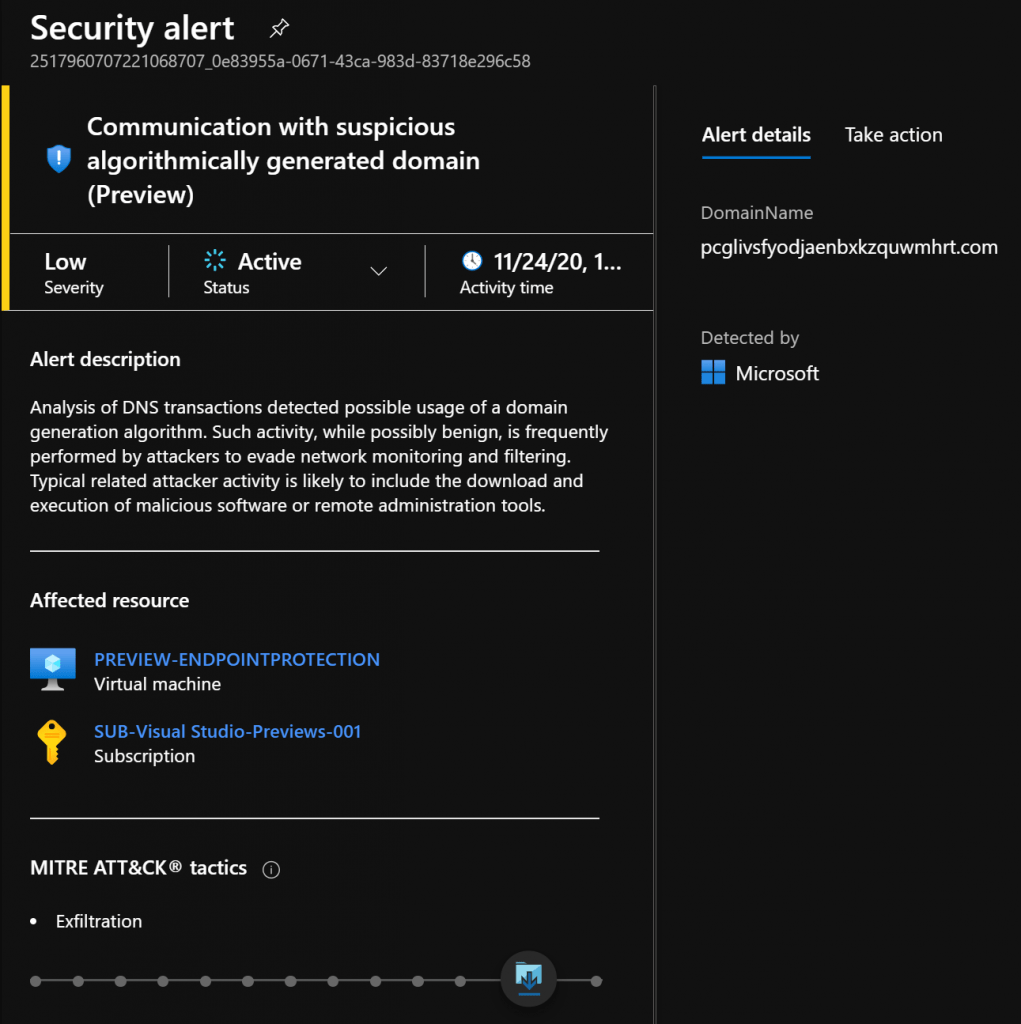
| Communication with suspicious algorithmically generated domain (AzureDNS_DomainGenerationAlgorithm) |
Analysis of DNS transactions from %{CompromisedEntity} detected possible usage of a domain generation algorithm. Such activity, while possibly benign, is frequently performed by attackers to evade network monitoring and filtering. Typical related attacker activity is likely to include the download and execution of malicious software or remote administration tools. | Exfiltration |
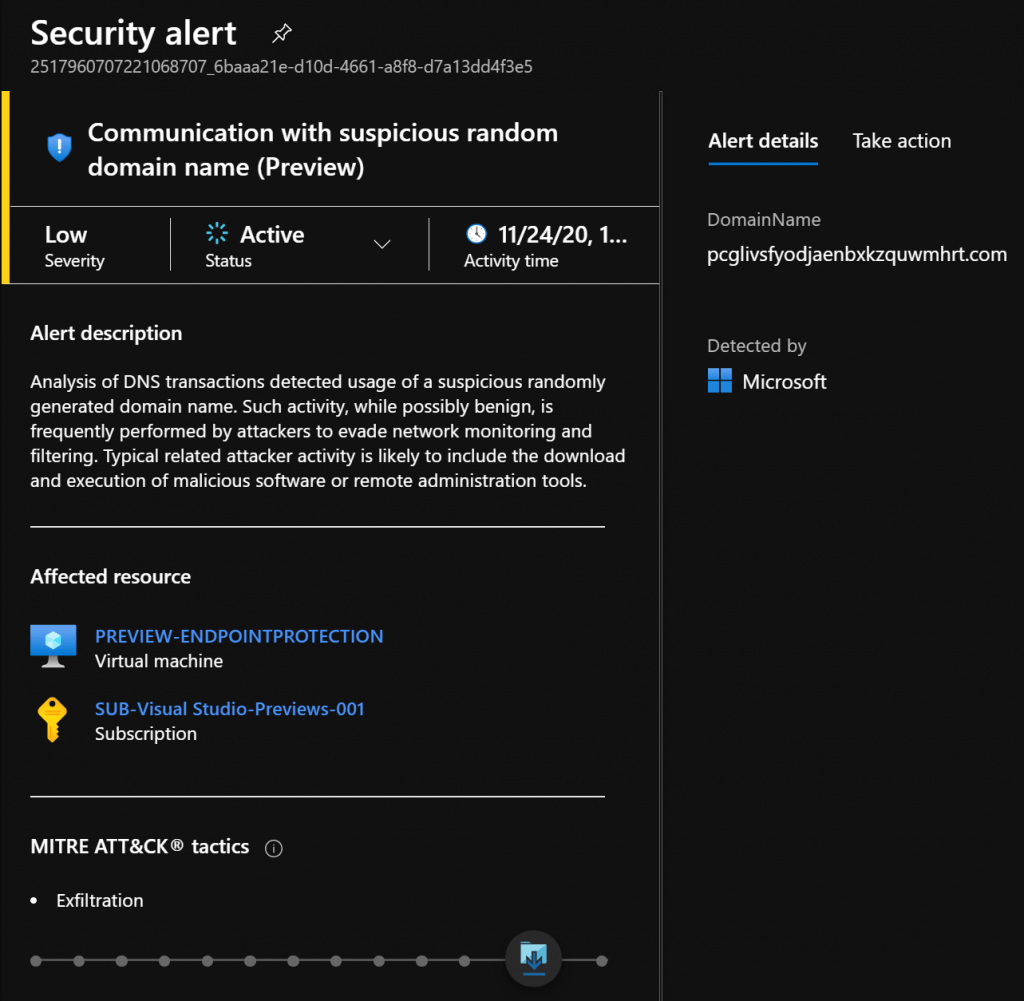
| Communication with suspicious random domain name (AzureDNS_RandomizedDomain) |
Analysis of DNS transactions from %{CompromisedEntity} detected usage of a suspicious randomly generated domain name. Such activity, while possibly benign, is frequently performed by attackers to evade network monitoring and filtering. Typical related attacker activity is likely to include the download and execution of malicious software or remote administration tools. | Exfiltration |
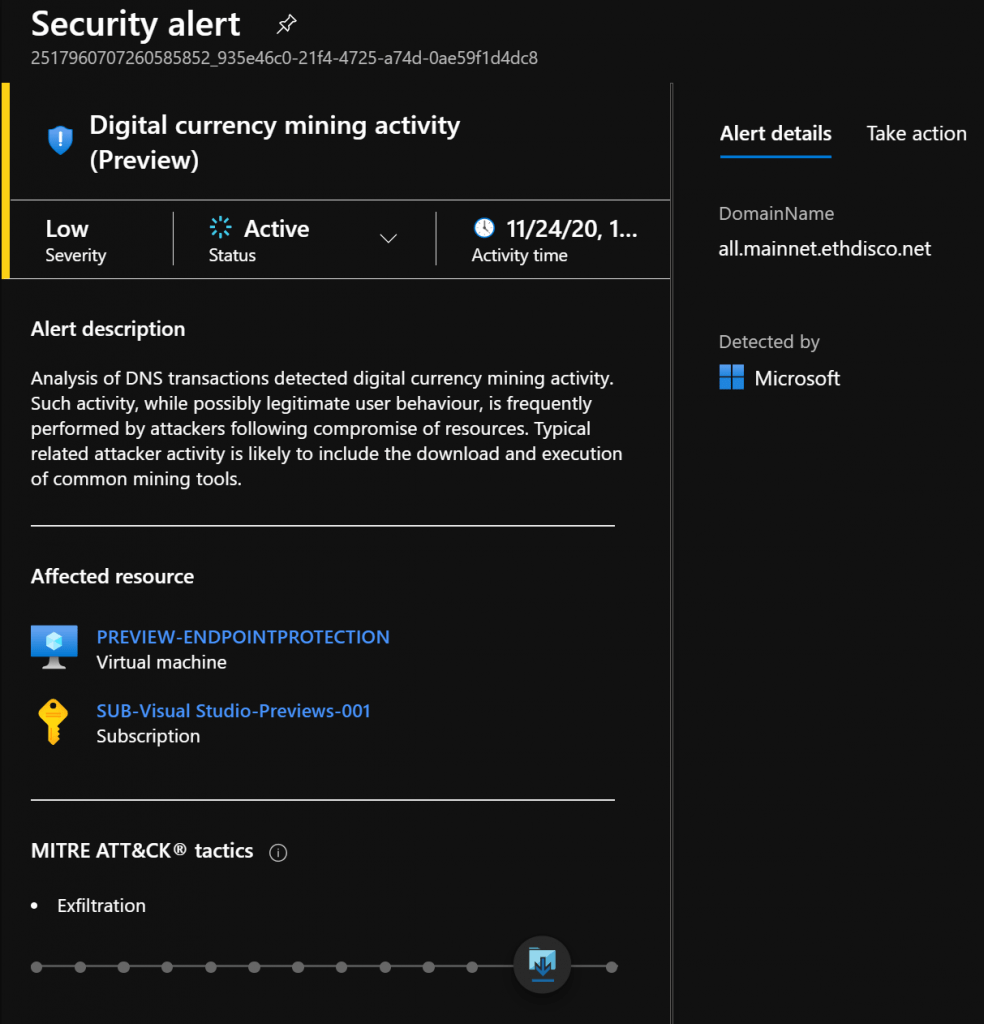
| Digital currency mining activity (AzureDNS_CurrencyMining) |
Analysis of DNS transactions from %{CompromisedEntity} detected digital currency mining activity. Such activity, while possibly legitimate user behaviour, is frequently performed by attackers following compromise of resources. Typical related attacker activity is likely to include the download and execution of common mining tools. | Exfiltration |
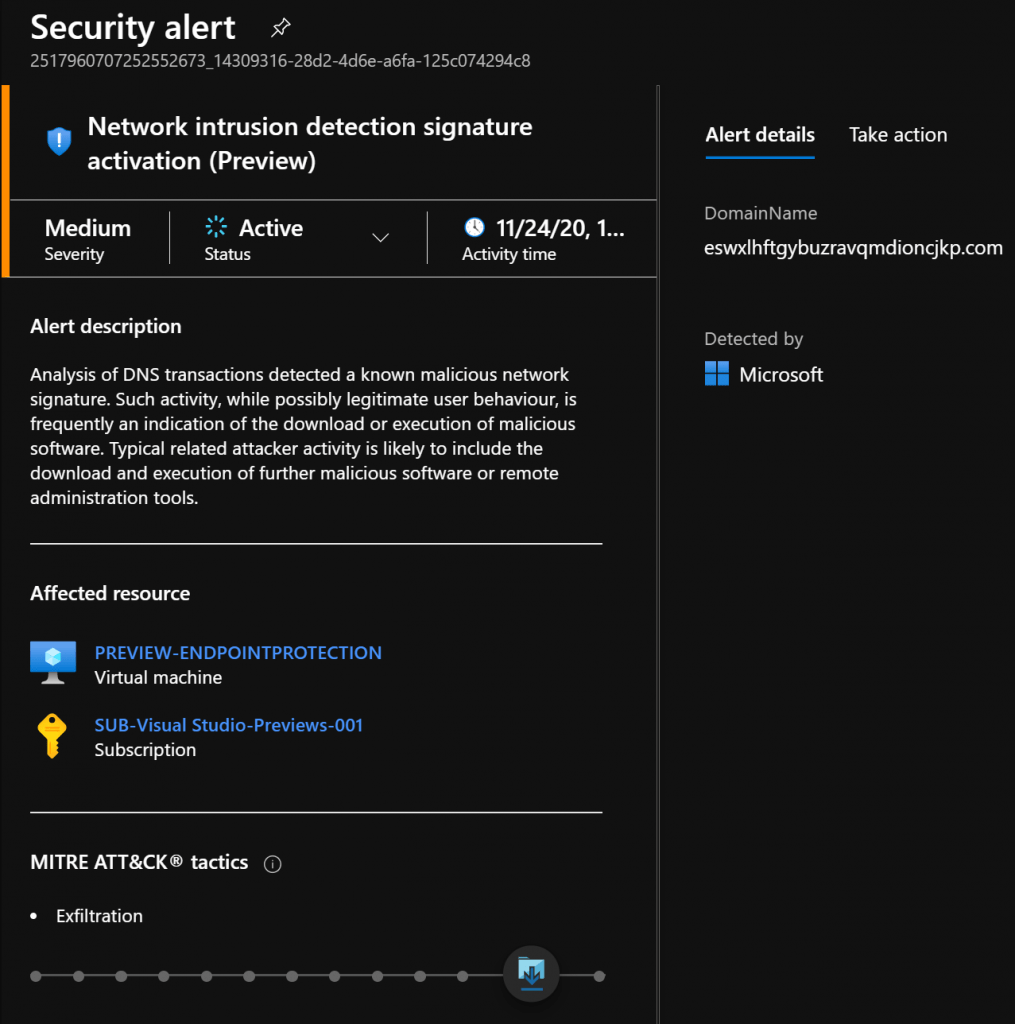
| Network intrusion detection signature activation (AzureDNS_SuspiciousDomain) |
Analysis of DNS transactions from %{CompromisedEntity} detected a known malicious network signature. Such activity, while possibly legitimate user behaviour, is frequently an indication of the download or execution of malicious software. Typical related attacker activity is likely to include the download and execution of further malicious software or remote administration tools. | Exfiltration |
| Possible data download via DNS tunnel (AzureDNS_DataInfiltration) |
Analysis of DNS transactions from %{CompromisedEntity} detected a possible DNS tunnel. Such activity, while possibly legitimate user behaviour, is frequently performed by attackers to evade network monitoring and filtering. Typical related attacker activity is likely to include the download and execution of malicious software or remote administration tools. | Exfiltration |
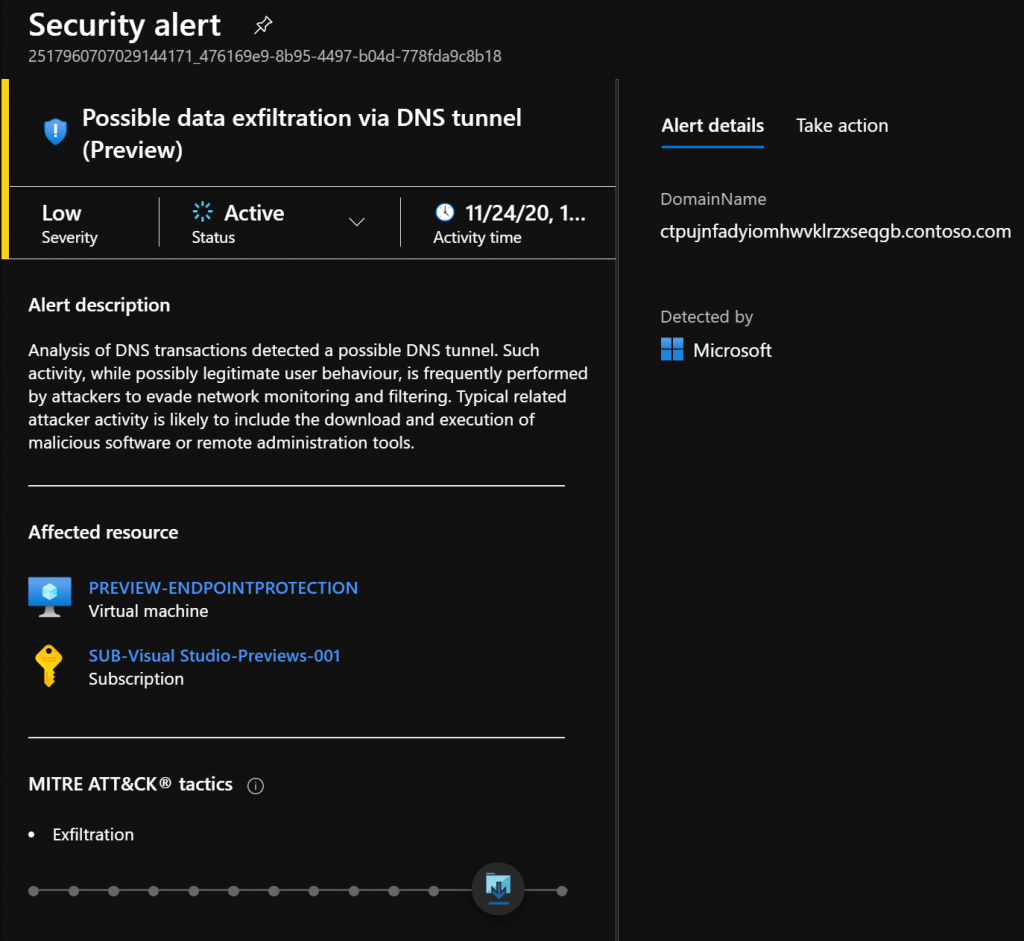
| Possible data exfiltration via DNS tunnel (AzureDNS_DataExfiltration) |
Analysis of DNS transactions from %{CompromisedEntity} detected a possible DNS tunnel. Such activity, while possibly legitimate user behaviour, is frequently performed by attackers to evade network monitoring and filtering. Typical related attacker activity is likely to include the download and execution of malicious software or remote administration tools. | Exfiltration |
| Possible data transfer via DNS tunnel (AzureDNS_DataObfuscation) |
Analysis of DNS transactions from %{CompromisedEntity} detected a possible DNS tunnel. Such activity, while possibly legitimate user behaviour, is frequently performed by attackers to evade network monitoring and filtering. Typical related attacker activity is likely to include the download and execution of malicious software or remote administration tools. | Exfiltration |
For more information about how to enable Azure Defender for DNS, see the instructions at link