Azure Defender provides security alerts and advanced threat protection for all kinds of workloads, like virtual machines, SQL databases, containers and web applications. New plans within Azure Defender are regularly introduced, recently for Key Vault and now also for Resource Manager (and DNS, see link).
The cloud management layer is a crucial service connected to all your cloud resources. Because of this, it is also a potential target for attackers. Consequently, it is recommended that security operations teams monitor the resource management layer closely.
Azure Defender for Resource Manager automatically monitors the resource management operations in your organization, whether they’re performed through the Azure portal, Azure REST APIs, Azure CLI, or other Azure programmatic clients. Azure Defender runs advanced security analytics to detect threats and alert you about suspicious activity.
Azure Defender for Resource Manager protects against issues including:
- Suspicious resource management operations, such as operations from suspicious IP addresses, disabling antimalware and suspicious scripts running in VM extensions
- Use of exploitation toolkits like Microburst or PowerZure
- Lateral movement from the Azure management layer to the Azure resources data plane
All of that without using any agents. The only thing you have to do is enable the Azure Defender plan for Resource Manager.
Alerts
A full list of the alerts provided by Azure Defender for Resource Manager:
| Alert | Description | Severity |
| Activity from a risky IP address (ARM.MCAS_ActivityFromAnonymousIPAddresses) | Users activity from an IP address that has been identified as an anonymous proxy IP address has been detected. These proxies are used by people who want to hide their device’s IP address, and can be used for malicious intent. This detection uses a machine learning algorithm that reduces false positives, such as mis-tagged IP addresses that are widely used by users in the organization. | Medium |
| Activity from infrequent country (ARM.MCAS_ActivityFromInfrequentCountry) | Activity from a location that wasn’t recently or ever visited by any user in the organization has occurred. This detection considers past activity locations to determine new and infrequent locations. The anomaly detection engine stores information about previous locations used by users in the organization. | Medium |
| Impossible travel activity (ARM.MCAS_ImpossibleTravelActivity) | Two user activities (in a single or multiple sessions) have occurred, originating from geographically distant locations. This occurs within a time period shorter than the time it would have taken the user to travel from the first location to the second. This indicates that a different user is using the same credentials. This detection uses a machine learning algorithm that ignores obvious false positives contributing to the impossible travel conditions, such as VPNs and locations regularly used by other users in the organization. The detection has an initial learning period of seven days, during which it learns a new user’s activity pattern. | Medium |
| Azurite toolkit run detected (ARM_Azurite) | A known cloud-environment reconnaissance toolkit run has been detected in your environment. The tool Azurite can be used by an attacker (or penetration tester) to map your subscriptions’ resources and identify insecure configurations. | High |
| Suspicious management session using PowerShell detected (ARM_UnusedAppPowershellPersistence) | Subscription activity logs analysis has detected suspicious behavior. A principal that doesn’t regularly use PowerShell to manage the subscription environment is now using PowerShell, and performing actions that can secure persistence for an attacker. | Medium |
| Suspicious management session using an inactive account detected (ARM_UnusedAccountPersistence) | Subscription activity logs analysis has detected suspicious behavior. A principal not in use for a long period of time is now performing actions that can secure persistence for an attacker. | Medium |
| MicroBurst toolkit “Get-AzureDomainInfo” function run detected (ARM_MicroBurstDomainInfo) | A known cloud-environment reconnaissance toolkit run has been detected in your environment. The tool “MicroBurst” (see https://github.com/NetSPI/MicroBurst) can be used by an attacker (or penetration tester) to map your subscription(s) resources, identify insecure configurations, and leak confidential information. | High |
| MicroBurst toolkit “Get-AzurePasswords” function run detected (ARM_MicroBurstRunbook) | A known cloud-environment reconnaissance toolkit run has been detected in your environment. The tool “MicroBurst” (see https://github.com/NetSPI/MicroBurst) can be used by an attacker (or penetration tester) to map your subscription(s) resources, identify insecure configurations, and leak confidential information. | High |
| Suspicious management session using Azure portal detected (ARM_UnusedAppIbizaPersistence) | Analysis of your subscription activity logs has detected a suspicious behavior. A principal that doesn’t regularly use the Azure portal (Ibiza) to manage the subscription environment (hasn’t used Azure portal to manage for the last 45 days, or a subscription that it is actively managing), is now using the Azure portal and performing actions that can secure persistence for an attacker. | Medium |
| Antimalware broad files exclusion in your virtual machine (ARM_AmBroadFilesExclusion) | Files exclusion from antimalware extension with broad exclusion rule was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Such exclusion practically disabling the Antimalware protection. Attackers might exclude files from the antimalware scan on your virtual machine to prevent detection while running arbitrary code or infecting the machine with malware. | Medium |
| Antimalware disabled and code execution in your virtual machine (ARM_AmDisablementAndCodeExecution) | Antimalware disabled at the same time as code execution on your virtual machine. This was detected by analyzing Azure Resource Manager operations in your subscription. Attackers disable antimalware scanners to prevent detection while running unauthorized tools or infecting the machine with malware. | High |
| Antimalware disabled in your virtual machine (ARM_AmDisablement) | Antimalware disabled in your virtual machine. This was detected by analyzing Azure Resource Manager operations in your subscription. Attackers might disable the antimalware on your virtual machine to prevent detection. | Medium |
| Antimalware file exclusion and code execution in your virtual machine (ARM_AmFileExclusionAndCodeExecution) | File excluded from your antimalware scanner at the same time as code was executed via a custom script extension on your virtual machine. This was detected by analyzing Azure Resource Manager operations in your subscription. Attackers might exclude files from the antimalware scan on your virtual machine to prevent detection while running unauthorized tools or infecting the machine with malware. | High |
| Antimalware file exclusion and code execution in your virtual machine (ARM_AmTempFileExclusionAndCodeExecution) | Temporary file exclusion from antimalware extension in parallel to execution of code via custom script extension was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Attackers might exclude files from the antimalware scan on your virtual machine to prevent detection while running arbitrary code or infecting the machine with malware. | High |
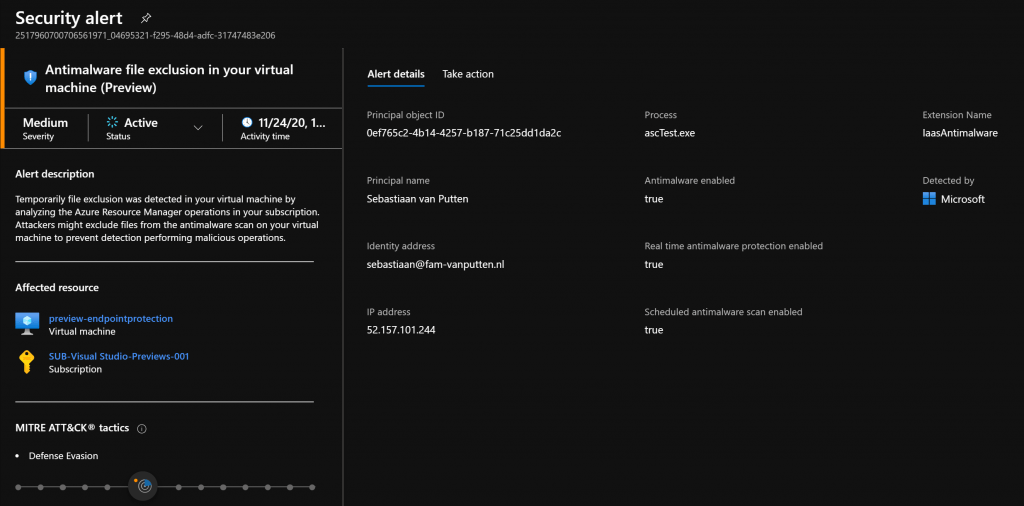
| Antimalware file exclusion in your virtual machine (ARM_AmTempFileExclusion) | File excluded from your antimalware scanner on your virtual machine. This was detected by analyzing Azure Resource Manager operations in your subscription. Attackers might exclude files from the antimalware scan on your virtual machine to prevent detection while running unauthorized tools or infecting the machine with malware. | Medium |
| Antimalware real-time protection was disabled in your virtual machine (ARM_AmRealtimeProtectionDisabled) | Real-time protection disablement of the antimalware extension was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Attackers might disable real-time protection from the antimalware scan on your virtual machine to avoid detection while running arbitrary code or infecting the machine with malware. | Medium |
| Antimalware real-time protection was disabled temporarily in your virtual machine (ARM_AmTempRealtimeProtectionDisablement) | Real-time protection temporary disablement of the antimalware extension was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Attackers might disable real-time protection from the antimalware scan on your virtual machine to avoid detection while running arbitrary code or infecting the machine with malware. | Medium |
| Antimalware real-time protection was disabled temporarily while code was executed in your virtual machine (ARM_AmRealtimeProtectionDisablementAndCodeExec) | Real-time protection temporary disablement of the antimalware extension in parallel to code execution via custom script extension was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Attackers might disable real-time protection from the antimalware scan on your virtual machine to avoid detection while running arbitrary code or infecting the machine with malware. | High |
| Antimalware temporarily disabled in your virtual machine (ARM_AmTemporarilyDisablement) | Antimalware temporarily disabled in your virtual machine. This was detected by analyzing Azure Resource Manager operations in your subscription. Attackers might disable the antimalware on your virtual machine to prevent detection. | Medium |
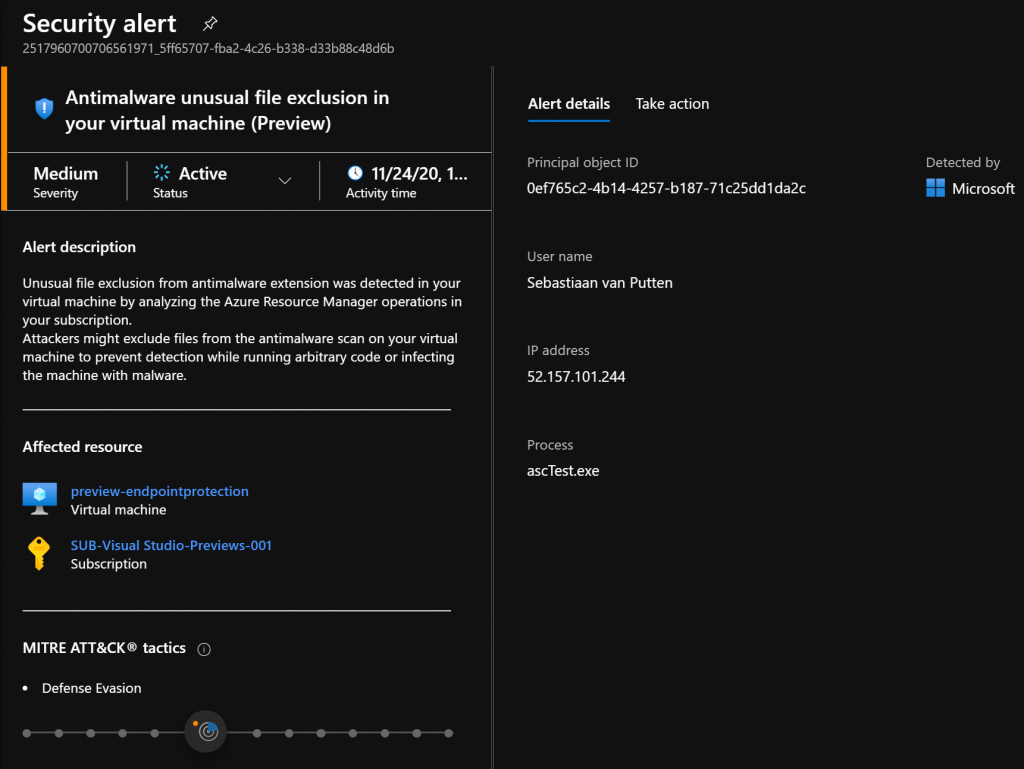
| Antimalware unusual file exclusion in your virtual machine (ARM_UnusualAmFileExclusion) | Unusual file exclusion from antimalware extension was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Attackers might exclude files from the antimalware scan on your virtual machine to prevent detection while running arbitrary code or infecting the machine with malware. | Medium |
| Custom script extension with suspicious command in your virtual machine (ARM_CustomScriptExtensionSuspiciousCmd) | Custom script extension with suspicious command was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Attackers may use custom script extension to execute a malicious code on your virtual machine via the Azure Resource Manager. | Medium |
| Custom script extension with suspicious entry-point in your virtual machine (ARM_CustomScriptExtensionSuspiciousEntryPoint) | Custom script extension with a suspicious entry-point was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. The entry-point refers to a suspicious GitHub repository. Attackers may use custom script extensions to execute malicious code on your virtual machines via the Azure Resource Manager. | Medium |
| Custom script extension with suspicious payload in your virtual machine (ARM_CustomScriptExtensionSuspiciousPayload) | Custom script extension with a payload from a suspicious GitHub repository was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Attackers may use custom script extensions to execute malicious code on your virtual machines via the Azure Resource Manager. | Medium |
| MicroBurst exploitation toolkit used to enumerate resources in your subscriptions (ARM_MicroBurst.AzDomainInfo) | MicroBurst’s Information Gathering module was run on your subscription. This tool can be used to discover resources, permissions and network structures. This was detected by analyzing the Azure Activity logs and resource management operations in your subscription | High |
| MicroBurst exploitation toolkit used to enumerate resources in your subscriptions (ARM_MicroBurst.AzureDomainInfo) | MicroBurst’s Information Gathering module was run on your subscription. This tool can be used to discover resources, permissions and network structures. This was detected by analyzing the Azure Activity logs and resource management operations in your subscription | High |
| MicroBurst exploitation toolkit used to execute code on your virtual machine (ARM_MicroBurst.AzVMBulkCMD) | MicroBurst’s exploitation toolkit was used to execute code on your virtual machines. This was detected by analyzing Azure Resource Manager operations in your subscription. | High |
| MicroBurst exploitation toolkit used to execute code on your virtual machine (RM_MicroBurst.AzureRmVMBulkCMD) | MicroBurst’s exploitation toolkit was used to execute code on your virtual machines. This was detected by analyzing Azure Resource Manager operations in your subscription. | High |
| MicroBurst exploitation toolkit used to extract keys from your Azure key vaults (ARM_MicroBurst.AzKeyVaultKeysREST) | MicroBurst’s exploitation toolkit was used to extract keys from your Azure key vaults. This was detected by analyzing Azure Activity logs and resource management operations in your subscription. | High |
| MicroBurst exploitation toolkit used to extract keys to your storage accounts (ARM_MicroBurst.AZStorageKeysREST) | MicroBurst’s exploitation toolkit was used to extract keys to your storage accounts. This was detected by analyzing Azure Activity logs and resource management operations in your subscription. | High |
| MicroBurst exploitation toolkit used to extract secrets from your Azure key vaults (ARM_MicroBurst.AzKeyVaultSecretsREST) | MicroBurst’s exploitation toolkit was used to extract secrets from your Azure key vaults. This was detected by analyzing Azure Activity logs and resource management operations in your subscription. | High |
| PowerZure exploitation toolkit used to elevate access from Azure AD to Azure (ARM_PowerZure.AzureElevatedPrivileges) | PowerZure exploitation toolkit was used to elevate access from AzureAD to Azure. This was detected by analyzing Azure Resource Manager operations in your tenant. | High |
| PowerZure exploitation toolkit used to enumerate resources (ARM_PowerZure.GetAzureTargets) | PowerZure exploitation toolkit was used to enumerate resources on behalf of a legitimate user account in your organization. This was detected by analyzing Azure Resource Manager operations in your subscription. | High |
| PowerZure exploitation toolkit used to enumerate storage containers, shares, and tables (ARM_PowerZure.ShowStorageContent) | PowerZure exploitation toolkit was used to enumerate storage shares, tables, and containers. This was detected by analyzing Azure Resource Manager operations in your subscription. | High |
| PowerZure exploitation toolkit used to execute a Runbook in your subscription (ARM_PowerZure.StartRunbook) | PowerZure exploitation toolkit was used to execute a Runbook. This was detected by analyzing Azure Resource Manager operations in your subscription. | High |
| PowerZure exploitation toolkit used to extract Runbooks content (ARM_PowerZure.AzureRunbookContent) | PowerZure exploitation toolkit was used to extract Runbook content. This was detected by analyzing Azure Resource Manager operations in your subscription. | High |
| Suspicious failed execution of custom script extension in your virtual machine (ARM_CustomScriptExtensionSuspiciousFailure) | Suspicious failure of a custom script extension was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Such failures may be associated with malicious scripts run by this extension. | Medium |
| Unusual config reset in your virtual machine (ARM_VMAccessUnusualConfigReset) | An unusual config reset was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. While this action may be legitimate, attackers can try utilizing VM Access extension to reset the configuration in your virtual machine and compromise it. | Medium |
| Unusual deletion of custom script extension in your virtual machine (ARM_CustomScriptExtensionUnusualDeletion) | Unusual deletion of a custom script extension was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Attackers may use custom script extensions to execute malicious code on your virtual machines via the Azure Resource Manager. | Medium |
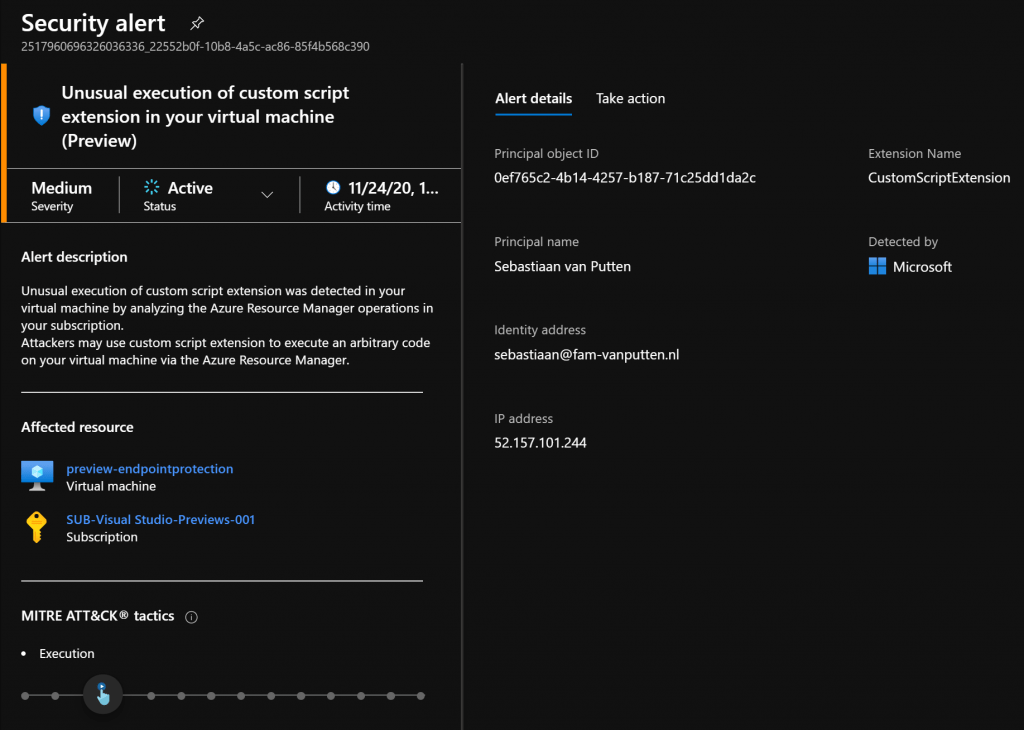
| Unusual execution of custom script extension in your virtual machine (ARM_CustomScriptExtensionUnusualExecution) | Unusual execution of a custom script extension was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. Attackers may use custom script extensions to execute malicious code on your virtual machines via the Azure Resource Manager. | Medium |
| Unusual user password reset in your virtual machine (ARM_VMAccessUnusualPasswordReset) | An unusual user password reset was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. While this action may be legitimate, attackers can try utilizing the VM Access extension to reset the credentials of a local user in your virtual machine and compromise it. | Medium |
| Unusual user SSH key reset in your virtual machine (ARM_VMAccessUnusualSSHReset) | An unusual user SSH key reset was detected in your virtual machine by analyzing the Azure Resource Manager operations in your subscription. While this action may be legitimate, attackers can try utilizing VM Access extension to reset SSH key of a user account in your virtual machine and compromise it. | Medium |
| Usage of MicroBurst exploitation toolkit to run an arbitrary code or exfiltrate Azure Automation account credentials (ARM_MicroBurst.RunCodeOnBehalf) | Usage of MicroBurst exploitation toolkit to run an arbitrary code or exfiltrate Azure Automation account credentials. This was detected by analyzing Azure Resource Manager operations in your subscription. | High |
| Usage of NetSPI techniques to maintain persistence in your Azure environment (ARM_NetSPI.MaintainPersistence) | Usage of NetSPI persistence technique to create a webhook backdoor and maintain persistence in your Azure environment. This was detected by analyzing Azure Resource Manager operations in your subscription. | High |
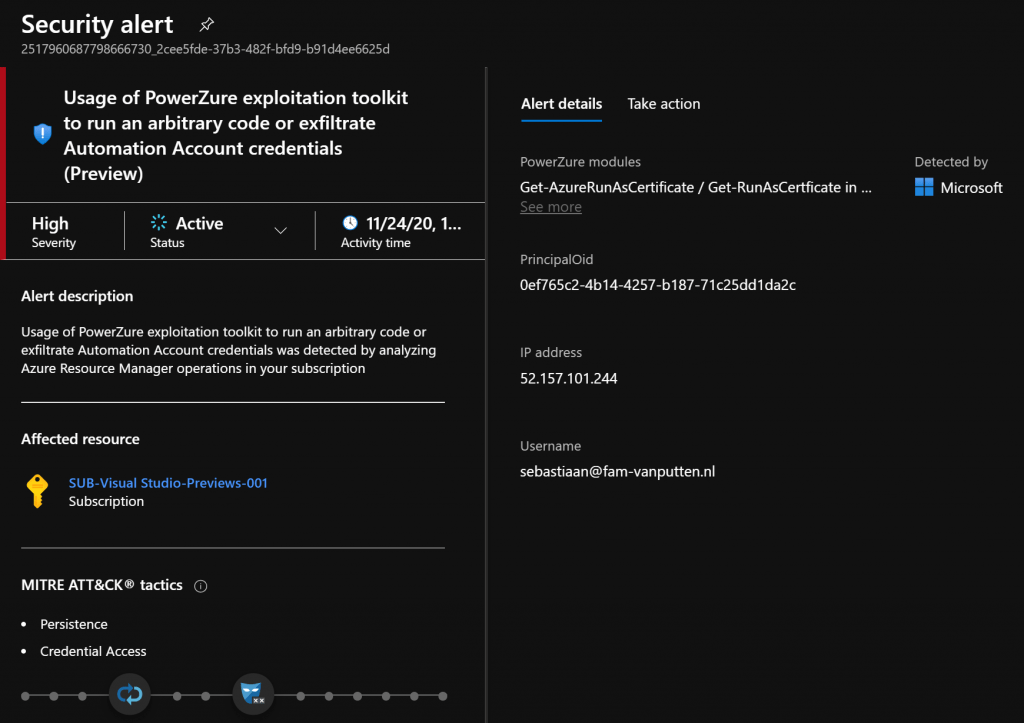
| Usage of PowerZure exploitation toolkit to run an arbitrary code or exfiltrate Azure Automation account credentials (ARM_PowerZure.RunCodeOnBehalf) | PowerZure exploitation toolkit detected attempting to run code or exfiltrate Azure Automation account credentials. This was detected by analyzing Azure Resource Manager operations in your subscription. | High |
| Usage of PowerZure function to maintain persistence in your Azure environment (ARM_PowerZure.MaintainPersistence) | PowerZure exploitation toolkit detected creating a webhook backdoor to maintain persistence in your Azure environment. This was detected by analyzing Azure Resource Manager operations in your subscription. | High |
For more information about how to enable Azure Defender for Resource Manager, see the instructions at link